Congress Preserves Vehicle Kill Switch Mandate: A Cybersecurity Analysis

Compliance Hub | January 24, 2026
Critical Infrastructure, Privacy & Attack Surface Analysis
Executive Summary
On January 22, 2026, the U.S. House of Representatives voted 164-268 to reject an amendment that would have defunded the federal vehicle "kill switch" mandate. The amendment, introduced by Rep. Thomas Massie (R-KY), sought to prohibit federal funding for Section 24220 of the Infrastructure Investment and Jobs Act (IIJA), which requires all new passenger vehicles manufactured after 2026 to include technology capable of detecting driver impairment and disabling the vehicle.
The vote saw 57 Republicans join 211 Democrats in opposition, highlighting significant bipartisan disagreement on the balance between highway safety and civil liberties. This analysis examines the cybersecurity implications, privacy concerns, and potential attack vectors introduced by mandating remote vehicle disabling technology in consumer automobiles.
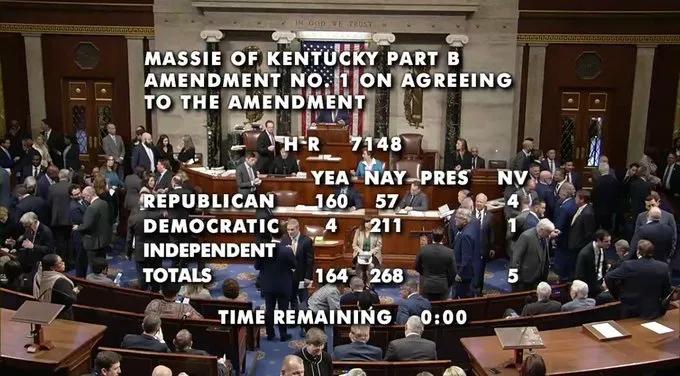
The Vote Breakdown
| Party | YEA | NAY | NV |
|---|---|---|---|
| Republican | 160 | 57 | 4 |
| Democratic | 4 | 211 | 1 |
| TOTALS | 164 | 268 | 5 |
Roll Call Reference: House Vote #43 - clerk.house.gov/Votes/202643
What Section 24220 Actually Requires
The 2021 Infrastructure Investment and Jobs Act contains specific language in Section 24220 mandating that:
"To ensure the prevention of alcohol-impaired driving fatalities, advanced drunk and impaired driving prevention technology must be standard equipment in all new passenger motor vehicles."
The legislation defines this technology as a system that can:
- Passively monitor the performance of a driver of a motor vehicle
- Passively monitor the blood alcohol concentration of a driver
- Prevent or limit motor vehicle operation if impairment is detected
The National Highway Traffic Safety Administration (NHTSA) is tasked with developing the specific implementation standards, with an original deadline of November 2024 for final rulemaking and enforcement beginning by September 2027.

Cybersecurity Attack Vectors
From a security perspective, mandating internet-connected vehicle disabling systems introduces significant attack surface considerations:
1. CAN Bus Vulnerabilities
Modern vehicles use Controller Area Network (CAN) buses dating back to the 1980s to connect critical systems including brakes, steering, and engine controls. The FBI's Internet Crime Complaint Center (IC3) has previously warned that connecting safety-critical components to the internet through infotainment systems represents a fundamental security flaw.
Key Risk: Any system capable of disabling a vehicle must interface with the CAN bus, creating a potential bridge from external networks to safety-critical controls.
2. Fleet-Wide Attack Potential
Unlike traditional vehicle theft or individual hacks, networked kill switch systems create the potential for mass-casualty cyberattacks. Research from Georgia Tech has modeled scenarios where:
- Simultaneously activating kill switches on millions of vehicles could shut down entire transportation networks
- Supply chain disruptions from disabled commercial vehicles could affect food, fuel, and medical supply delivery
- A Consumer Watchdog report estimated a fleet-wide hack could cause approximately 3,000 deaths from a single coordinated breach
3. Remote Exploitation Pathways
Security researchers have documented multiple attack vectors against connected vehicles:
| Attack Vector | Risk Level | Example |
|---|---|---|
| Cellular/Telematics | Critical | 2015 Jeep Cherokee hack - 1.4M vehicles recalled |
| Mobile Apps | High | Kaspersky found vulnerabilities in apps with 1M+ downloads |
| OBD-II Ports | High | Direct CAN bus access through diagnostic ports |
| GPS/Immobilizer Systems | High | Default password vulnerabilities in commercial trackers |
| OTA Updates | Medium | Malicious firmware delivery via compromised update channels |
| Bluetooth/WiFi | Medium | Proximity-based exploitation |
4. Third-Party Data Access
The technology required for impairment detection necessarily involves continuous monitoring systems. This creates concerns about:
- Insurance company access to driving behavior data
- Law enforcement data requests without traditional warrant processes
- Manufacturer data collection for commercial purposes
- Foreign adversary targeting of transportation infrastructure

The Privacy Dimension
Rep. Harriet Hageman (R-WY) characterized the mandate as "a massive and likely unconstitutional rule and an invasion of privacy on a greater scale than we are used to seeing from our government."
Passive Monitoring Concerns
The legislation explicitly requires "passive monitoring" capabilities, meaning the system continuously observes driver behavior without active driver participation. Proposed implementation methods include:
- In-cabin cameras monitoring eye movement and facial expressions
- Steering pattern analysis detecting erratic movements
- Breath/air sensors measuring alcohol content in the vehicle cabin
- Touch-based BAC sensors in steering wheels or start buttons
Due Process Questions
Rep. Massie raised fundamental due process concerns: "When your car shuts down because it doesn't approve of your driving, how will you appeal your roadside conviction?"
Unlike traditional DUI enforcement, which involves:
- Officer observation and probable cause
- Field sobriety testing
- Chemical testing with chain of custody
- Judicial review and legal representation
Automated vehicle disabling operates as algorithmic enforcement with no immediate appeal mechanism, no human judgment, and potential for false positives from medical conditions, fatigue, or system malfunctions.
House rules are complicated and not well understood, even by many of my colleagues.
— Thomas Massie (@RepThomasMassie) January 23, 2026
Every Republican who voted for the DHS bill, which was every one but me, enabled gender affirming care earmarks and the automobile kill switch mandate to pass the House.https://t.co/ykLyE8tAZG pic.twitter.com/65oTnHewS4
The 57 Republicans Who Voted Against Defunding
The following Republican representatives joined Democrats in preserving the kill switch mandate funding:
| Representative | State | Representative | State |
|---|---|---|---|
| Mark Amodei | NV-02 | French Hill | AR-02 |
| Don Bacon | NE-02 | Jeff Hurd | CO-03 |
| Stephanie Bice | OK-05 | Brian Jack | GA-03 |
| Gus Bilirakis | FL-12 | John James | MI-10 |
| Mike Bost | IL-12 | David Joyce | OH-14 |
| Ken Calvert | CA-41 | Thomas H. Kean Jr. | NJ-07 |
| John Carter | TX-31 | Mike Kelly | PA-16 |
| Tom Cole | OK-04 | Jen Kiggans | VA-02 |
| Mario Diaz-Balart | FL-26 | Kevin Kiley | CA-03 |
| Neal Dunn | FL-02 | Young Kim | CA-40 |
| Chuck Edwards | NC-11 | Kimberlyn King-Hinds | MP-AL |
| Jake Ellzey | TX-06 | Darin LaHood | IL-16 |
| Randy Feenstra | IA-04 | Nick LaLota | NY-01 |
| Randy Fine | FL-06 | Mike Lawler | NY-17 |
| Chuck Fleischmann | TN-03 | Frank D. Lucas | OK-03 |
| Vince Fong | CA-20 | Nicole Malliotakis | NY-11 |
| Brian Fitzpatrick | PA-01 | Celeste Maloy | UT-02 |
| Andrew Garbarino | NY-02 | Brian Mast | FL-21 |
| Carlos Gimenez | FL-28 | Dan Meuser | PA-09 |
| Max Miller | OH-07 | Maria Elvira Salazar | FL-27 |
| Mariannette Miller-Meeks | IA-01 | Mike Simpson | ID-02 |
| Blake D. Moore | UT-01 | Elise Stefanik | NY-21 |
| Tim Moore | NC-14 | Glenn "GT" Thompson | PA-15 |
| James C. Moylan | GU-AL | Michael R. Turner | OH-10 |
| Greg Murphy | NC-03 | David Valadao | CA-22 |
| Dan Newhouse | WA-04 | Derrick Van Orden | WI-03 |
| Zach Nunn | IA-03 | Rob Wittman | VA-01 |
| Harold Rogers | KY-05 | Steve Womack | AR-03 |
| Ryan Zinke | MT-01 |
Note: Representatives Hunt (TX), McClintock (CA), and Radewagen (American Samoa) were recorded as "Not Voting."
The Safety Argument
Proponents of the mandate cite significant public safety benefits:
- 13,000+ deaths annually from alcohol-impaired driving crashes (approximately 31% of all traffic fatalities)
- Rep. Debbie Wasserman Schultz (D-FL) argued passive drunk driving technology is "a key way to protect family members and others sharing the roadways"
- MADD (Mothers Against Drunk Driving) has championed this technology for decades
However, critics note the legislation does not define:
- What constitutes "impairment" beyond alcohol
- How the system distinguishes medical emergencies from intoxication
- What happens when the system incorrectly detects impairment at highway speeds
- How autonomous systems will gradually disable vehicles safely
Compliance & Industry Implications
For Automotive Manufacturers
Vehicle manufacturers face significant compliance requirements:
- Integration of passive monitoring systems into all new passenger vehicles
- CAN bus security hardening to prevent exploitation of disabling capabilities
- Data retention and access policies for monitoring data
- Liability frameworks for false positives and system failures
- Over-the-air update security for safety-critical systems
For Fleet Operators
Commercial fleet operators should consider:
- Enhanced telematics security audits
- Segmentation of safety-critical vehicle networks
- Incident response planning for fleet-wide disable scenarios
- Insurance implications of mandated kill switch systems
- Driver privacy policies for continuous monitoring data
For Cybersecurity Professionals
Security teams should prepare for:
- New vulnerability classes in automotive systems
- Expanded attack surfaces in connected vehicle infrastructure
- Critical infrastructure protection considerations for transportation
- Penetration testing frameworks for automotive systems
- Incident response protocols for vehicle-based attacks
What Happens Next
The larger $1.2 trillion spending package (H.R. 7148) passed the House 341-88 and now moves to the Senate for consideration before the January 30 deadline. The Massie amendment's failure means:
- NHTSA retains funding to develop implementation standards
- The 2026/2027 mandate timeline remains on track
- Separate legislation (the "No Kill Switches in Cars Act") remains in committee
- State-level pushback may emerge, with Florida Gov. Ron DeSantis already criticizing the mandate
Recommendations for Organizations
Immediate Actions
- Inventory connected vehicle assets and assess kill switch exposure
- Review fleet telematics security configurations and access controls
- Establish monitoring for automotive CVE disclosures
- Update incident response plans to include vehicle-based scenarios
Strategic Considerations
- Evaluate vehicle procurement policies considering security implications
- Engage with automotive vendors on security roadmaps
- Consider air-gapped alternatives for sensitive operations
- Monitor regulatory developments at federal and state levels
Conclusion
The preservation of funding for Section 24220's vehicle kill switch mandate represents a significant expansion of connected vehicle requirements with substantial cybersecurity implications. While the technology aims to address the genuine public safety crisis of impaired driving, the implementation introduces attack vectors, privacy concerns, and due process questions that security professionals, fleet operators, and individual consumers must carefully consider.
The 164-268 vote demonstrates this remains a contentious issue crossing traditional party lines. As implementation moves forward, the cybersecurity community should prepare for new vulnerability classes, expanded attack surfaces, and critical infrastructure protection challenges in the automotive sector.
For more cybersecurity compliance analysis, visit Compliance Hub
Related Resources:
- House Roll Call Vote #43
- H.R. 7148 - Consolidated Appropriations Act, 2026
- Section 24220 - Infrastructure Investment and Jobs Act
- NHTSA Advanced Impaired Driving Prevention Technology Report
- IC3 - Motor Vehicles Vulnerable to Remote Exploits
© 2026 CISO Marketplace / Compliance Hub. All rights reserved.